Sql Injection Tool Get Cc Cvv Dob
SQL injection is one of the most common attacks against web applications. This is used against websites which use SQL to query data from the database server. A successful SQL injection attack can read sensitive data including email, username, password, and credit card details from your database.
.Dob + SSN + ) Banks logins, Paypal verified, Ebay, Amazon accounts logins, bestbuy, all kinds of shops account available. Sql Injection Tool Get Cc Cvv.
An attacker can not only read, but also modify or delete the data from the database. So, SQL injection can be very harmful.There are various kinds of SQL injection which are defined based on scope. These are:. Classic SQL injection. Blind SQL injection. Database specific SQL injection.
- SQL Injection Forum Hacking & Exploit Tutorial - SQLiWiki SQL Injection Tutorial MSSQL Tutorial SELL CVV COUNTRIES: USA, UK, CA, AU, EU, INTER, ASIAN AND MORE OTHER COUNTRIES Thread Modes.
- After that open your Command Promp (CMD) Type cd And then press ENTER Type cd sqlmap And Enter Copy your victim link And type to cmd like this sqlmap.py -u -dbs Replace to your link target Enter! SQL Injection - Tool Get CC-CVV (3 Tables).
Compound SQLII am not going into details of these classes. We have covered various tutorials on SQL injection in the past. You can explore our resources by using the search feature.SQL injection vulnerability exists because developers do not care about data validation and security. Users’ input must be sanitized before passing into SQL queries, but developers forget to do this or do not properly sanitize. This makes the web application vulnerable to SQL injection attack.Performing classic SQL injection is easy via browser based attack by injecting queries in various parameters.
But it also requires knowledge of SQL queries. For blind SQL injection or another, you need to be an expert with high knowledge of database queries, database architecture and experience. And using manual ways takes a lot of time.To make the SQL injection attack process easy, developers have also developed SQL injection tools by creating a good detection engine. With every new release, these tools are becoming smarter. These tools take the vulnerable URL as a parameter and then start attacking the target.
Based on its detection and attack engine, these tools are capable of detecting the type of attack. Sometimes, a vulnerable URL is protected via session and requires login. So, these tools have also gotten the capability of login into a web application via provided username and password to perform SQL injection in the target application.
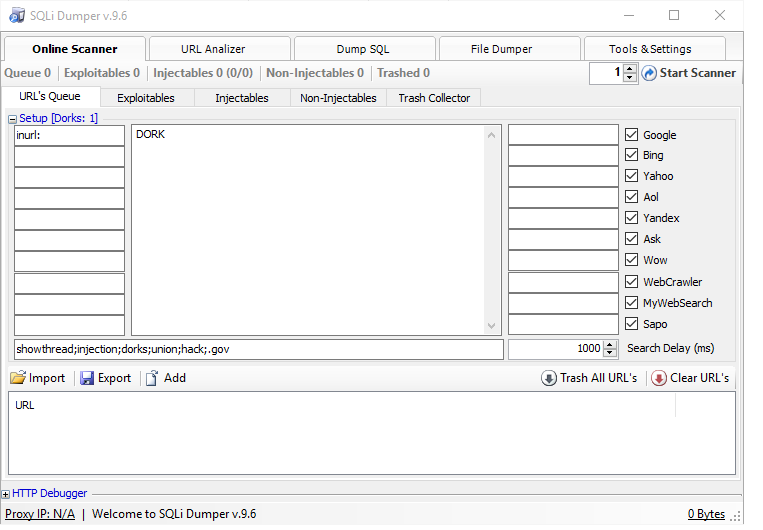
These tools can perform GET-based, POST-based or cookie-based SQL injection without any problem.These tools can automatically perform an attack, and in a few minutes, you will get a successful attack result. These tools also allow you to access any table or any column of the database in just a click and attack process. In CLI tools, you can use commands to access data. These tools also let you run SQL queries in the target database.
So, you can access, modify or delete data on the target server. These tools also allow attackers to upload or download files from the server.In this post, we are adding few open source SQL injection tools.
These tools are powerful and can perform automatic SQL injection attacks against the target applications. I will also add the download link to download the tool and try. I tried my best to list the best and most popular SQL injection tools.
BSQL HackerBSQL hacker is a nice SQL injection tool that helps you perform a SQL injection attack against web applications. This tool is for those who want an automatic SQL injection tool. It is especially made for Blind SQL injection. This tool is fast and performs a multi-threaded attack for better and faster results.It supports 4 different kinds of SQL injection attacks:. Blind SQL Injection. Time Based Blind SQL Injection.
Deep Blind (based on advanced time delays). SQL Injection Error Based SQL InjectionThis tool works in automatic mode and can extract most of the information from the database.
It comes in both GUI and console support. You can try any of the given UI modes. From GUI mode, you can also save or load saved attack data.It supports multiple injection points including query string, HTTP headers, POST, and cookies.
It supports a proxy to perform the attack. It can also use the default authentication details to login into web accounts and perform the attack from the given account. It supports SSL protected URLs, and can also be used on SSL URLs with invalid certificates.BSQL Hacker SQL injection tool supports MSSQL, ORACLE and MySQL. But MySQL support is experimental and is not as effective on this database server as it is for other two.Download BSQL Hacker here. SQLmapSQLMap is the open source SQL injection tool and most popular among all SQL injection tools available.
This tool makes it easy to exploit the SQL injection vulnerability of a web application and take over the database server. It comes with a powerful detection engine which can easily detect most of the SQL injection related vulnerabilities.It supports a wide range of database servers, including MySQL, Oracle, PostgreSQL, Microsoft SQL Server, Microsoft Access, IBM DB2, SQLite, Firebird, Sybase, SAP MaxDB and HSQLDB. Most of the popular database servers are already included. It also supports various kind of SQL injection attacks, including boolean-based blind, time-based blind, error-based, UNION query-based, stacked queries and out-of-band.One good feature of the tool is that it comes with a built-in password hash recognition system.
It helps in identifying the password hash and then cracking the password by performing a dictionary attack.This tool allows you to download or upload any file from the database server when the db server is MySQL, PostgreSQL or Microsoft SQL Server. And only for these three database servers, it also allows you to execute arbitrary commands and retrieve their standard output on the database server.After connecting to a database server, this tool also lets you search for specific database name, specific tables or for specific columns in the whole database server. This is a very useful feature when you want to search for a specific column but the database server is huge and contains too many databases and tables.Download SQL Map from the link given below:SQLninjaSQLninja is a SQL injection tool that exploits web applications that use a SQL server as a database server. This tool may not find the injection place at first. But if it is discovered, it can easily automate the exploitation process and extract the information from the database server.This tool can add remote shots in the registry of the database server OS to disable data execution prevention. The overall aim of the tool is to allow the attacker to gain remote access to a SQL database server.It can also be integrated with Metasploit to get GUI access to the remote database.
It also supports direct and reverse bindshell, both TCP and UDP.This tool is not available for Windows platforms. It is only available for Linux, FreeBSD, Mac OS X and iOS operating systems.Download SQLninja from the link given below:Safe3 SQL InjectorSafe3 SQL injector is another powerful but easy to use SQL injection tool. Like other SQL injection tools, it also makes the SQL injection process automatic and helps attackers in gaining the access to a remote SQL server by exploiting the SQL injection vulnerability. It has a powerful AI system which easily recognizes the database server, injection type and best way to exploit the vulnerability.It supports both HTTP and HTTPS websites. You can perform SQL injection via GET, POST or cookies. It also supports authentication (Basic, Digest, NTLM HTTP authentications) to perform a SQL injection attack. The tool supports wide range of database servers including MySQL, Oracle, PostgreSQL, Microsoft SQL Server, Microsoft Access, SQLite, Firebird, Sybase and SAP MaxDB database management systems.For MYSQL and MS SQL, it also supports read, list or write any file from the database server.
It also lets attackers execute arbitrary commands and retrieve their output on a database server in Oracle and Microsoft SQL server. It also support web path guess, MD5 crack, domain query and full SQL injection scan.Download Safe3 SQL injector tool from the link given below:SQLSusSQLSus is another open source SQL injection tool and is basically a MySQL injection and takeover tool. This tool is written in Perl and you can extend the functions by adding your own codes. This tool offers a command interface which lets you inject your own SQL queries and perform SQL injection attacks.This tool claims to be fast and efficient. It claims to use a powerful blind injection attack algorithm to maximize the data gathered. For better results, it also uses stacked subqueries. To make the process even faster, it has multi-threading to perform attacks in multiple threads.Like other available SQL injection tools, it also supports HTTPS.
It can perform attacks via both GET and POST. It also supports, cookies, socks proxy, HTTP authentication, and binary data retrieving.If the access to informationschema is not possible or table does not exist, it can perform a bruteforce attack to guess the name of the table. With this tool, you can also clone a database, table, or column into a local SQLite database, and continue over different sessions.If you want to use a SQL injection tool against a MySQL attack, you will prefer this tool because it is specialized for this specific database server.Download SQLsus from the link given below:MoleMole or (The Mole) is an automatic SQL injection tool available for free. This is an open source project hosted on Sourceforge. You only need to find the vulnerable URL and then pass it in the tool. This tool can detect the vulnerability from the given URL by using Union based or Boolean based query techniques.
This tool offers a command line interface, but the interface is easy to use. It also offers auto-completion on both commands and command arguments. So, you can easily use this tool.Mole supports MySQL, MsSQL and Postgres database servers.
Sql Injection Tool Get Cc Cvv Dob Online
So, you can only perform SQL injection attacks against these databases. This tool was written in Python and requires only Python3 and Python3-lxml.
This tool also supports GET, POST and cookie based attacks. But you need to learn commands to operate this tool. Commands are not typical but you need to have them. List those commands or learn, it is your personal choice.Download Mole SQL injection tool from the link below:Ethical Hacking Boot Camp — Exam Pass Guarantee ConclusionThese are a few automatic SQL injection tools which you can try to perform a SQL injection attack.
In case I missed any, please share it with us via comments. Aew of these tools also come with penetration testing specific operating systems. If you are using Backtrack or Kali Linux, you already have a few of these tools. So, you can try them in those operating systems.Note: We do not encourage any illegal activity with these tools. Use these tools only for learning purposes and perform only on websites you own. We will not be responsible for any damage you cause with these tools.
DetailsRating: 5/5Price: FreeSQL Ninja is a powerful SQL server injection and takeover tool that offers great support to penetration testers. With this application, penetration testers are able to remotely take over a DB whenever a vulnerability has been detected. Thus a solution for the web applications that uses Microsoft SQL as their backend.
You can also seeWhat is SQL Injection Tool?An SQL Injection Tool is a computer program that allows developing and maintaining web applications to detect and manage the vulnerable points. These are particularly those applications that make use of SQL databases for their various applications. SQL injection is a penetration mechanism that hackers use to send a query to your database and consequently dump the content of your database to their disposal. You can also seeAt the same time, it can be used to deposit some unwanted files into the database. In the majority of the cases, the tools used for scanning these injections also come with takeover functionality.
This is what controls the app when an intrusion is detected.Ensuring the security of your web-based applications is fundamental as it ensures it will continue to perform optimally. With the use of the tools we have reviewed, you will be able to settle on an ideal penetration testing tool and thus guarantee the safety of your data as well as the users of the app.